This is a guest post by Gary Stevens.
Gary Stevens is a front end developer. He’s a full time blockchain geek and a volunteer working for the Ethereum foundation as well as an active Github contributor.
As the most popular web publishing platform and content management system in the world, WordPress has many features that web designers, developers, and administrators have come to love over the years. But such widespread popularity brings with it some major security concerns.
The security issues involving WordPress are similar to the ones that plague Microsoft Windows.
In Windows, we have an extremely popular operating system that was developed by some of the best engineers in the world, and yet, it seems like a new security vulnerability is discovered in it every day.
There’s a good explanation for that, and it’s directly tied to the operating system’s massive market share. Hackers know that millions of computers around the world run on Windows, and this makes it a very big target. At any given moment, countless cybercrime groups are actively working on new security exploits against Windows, and the same can be said about WordPress.
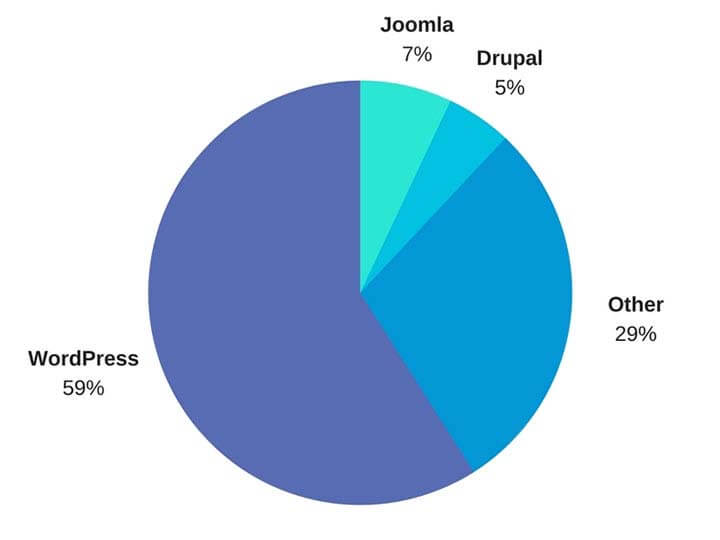
According to Digital.com, a renowned hosting guide website based in Melbourne, WordPress is the publishing platform that powers 26.4% of the internet. Every six months, a little more than one million new WordPress domains are registered. In terms of CMS market share, WP enjoys nearly 60 per cent, which puts it way above Joomla!, its main competitor.
Recent WordPress Security Failures
History tells us that a system with very high usage and market share like WordPress presents an attractive target for hackers. Recent news also helps prove this point:
- In its 2018 cyber intrusion report, the information security firm, CrowdStrike, described how a single compromised laptop brought down the entire network of a well-known apparel brand. The breach exploited a vulnerability that was specifically coded to affect WP sites.
- In November 2018, antivirus developer, Sophos, reported that the WP plugin developed for compliance with the European Union’s General Protection Data Regulation (GDPR) was hacked by means of an admin-ajax.php attack. Through this exploit, hackers were able to, not only inject malware, but also create WP admin accounts for the purpose of gaining full control of the back-end.
Known WordPress Vulnerabilities
In 2019, WP administrators and developers should keep in mind that security risks will continue to be elevated. New vulnerabilities will be discovered regularly, so it’s important that administrators keep their sites safe by addressing known issues.
The rest of this section describes some known vulnerabilities to watch out for.
WP SEO Spy Plugin
Plugin components are responsible for the most common vulnerabilities used by WP hackers, and some of the oldest plugins are among the worst offenders.
The SEO Spy plugin is worth calling out because it includes a Flash library that has been deprecated since 2009. Flash, due to its inherent security problems, is not used much anymore. Following that trend, the makers of the SEO Spy plugin abandoned it and stopped providing updates. Make sure you don’t have this long-forgotten but dangerous plugin installed on your site.
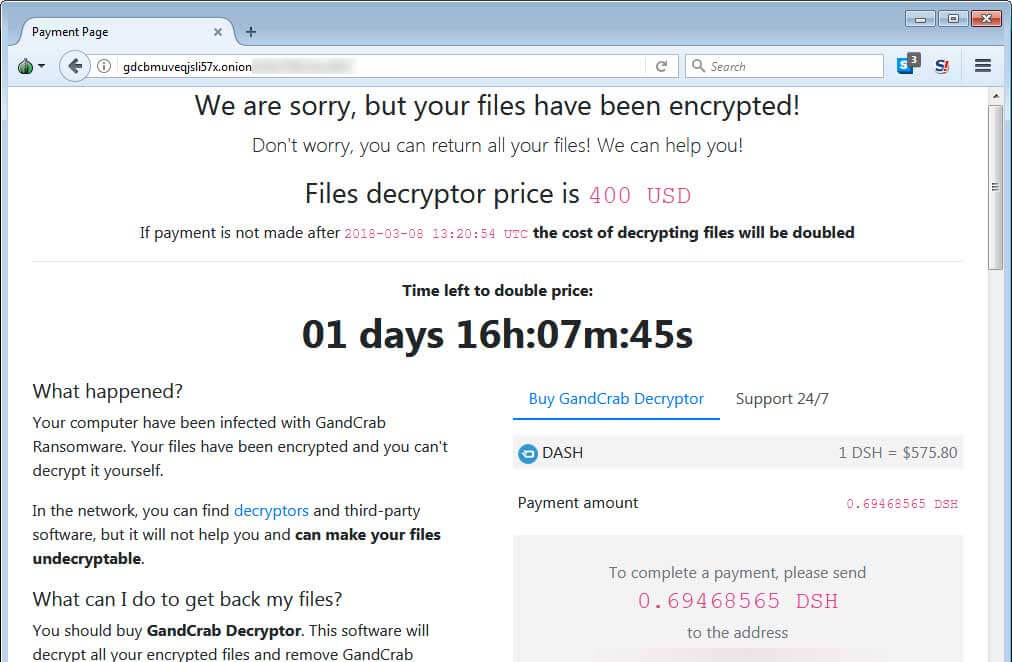
GandCrab Ransomware
Over the last two years, ransomware attacks have made shocking news headlines, and this cybercrime trend is bound to continue in 2019. The GandCrab ransomware was first detected in July 2018 and was found to have infected quite a few WordPress sites.
Security researchers have traced many of the GandCrab attacks to Russian cybercrime groups. The criminals’ tactics involve issuing invalid keys as a way of reversing file encryption after ransom payments are received. The best protection against ransomware attacks is to have a reliable data backup strategy.
PHP Object Injection
This authentication and serialization attack is related to a couple of vulnerabilities, one of them involving the Google Forms plugin, and the other, an injection of malicious PHP code.
Thankfully, these issues were widely discussed at the Black Hat USA 2018 conference. They were promptly addressed by the time WordPress version 5.0.1 was released later that year. In 2019, the best defense against PHP object injection attacks on WP is to update to version 5.0.1.
PHPMailer Remote Code Execution
Quite a few of the security risks that affect WordPress can be avoided by using only the most recent version of the CMS and ensuring that all plugin components are up to date. PHPMailer’s weakness dates back to 2016, and was quite infamous because it impacted thousands of websites.
The security holes have been fixed, but, these days, there are similar WP plugins that get better reviews than PHPMailer, so you might as well avoid this problematic plugin.
Hacked WP Login Credentials
This weakness can’t be blamed on WordPress. It’s the result of poor security practices among administrators and content creators. As previously mentioned, hackers are constantly looking for ways to break into WP sites, and they do so by monitoring public, and even private, Wi-Fi networks.
Webmasters who manage a site’s backend CMS, either from their personal machine, or from a company network, should encrypt traffic over a virtual private network (VPN) during remote admin sessions. Failure to use basic encryption leaves your connection exposed to rudimentary cyber attacks, meaning hackers could gain access to your CMS.
Pike Firewall
This is another plugin that can be problematic if it’s not configured correctly. There’s nothing fundamentally wrong with the Pike Firewall; problems arise when users unintentionally modify its settings to allow anonymous traffic to access the administration panel.
A WP firewall should never be considered a replacement for a traditional server firewall. They’re useful as traffic blocking plugins, but they need to be carefully configured to achieve the desired result.
Insider Attacks with Malicious Code Injection
Although this vulnerability is not directly related to the WordPress core, the system’s developers have taken steps to address it in version 5.0.1. Even with the newly added safeguards, the best way for administrators to prevent in-house malicious code injection is by having a good relationship with co-workers, partners, and content creators.
Know who has access to your system, and what they have permission to do. A PHP-savvy CMS user whose credentials allow them to do as little as delete image thumbnails, for example, may still be able to inject malicious code, and you’ll never know who did it.
The Bottom Line
While it might seem like WordPress has more than its fair share of security vulnerabilities, it’s the biggest player in content management, and, as with Windows, hackers tend to target systems with the most users.
The bottom line is, there’s no reason to worry about security weaknesses in WordPress. Security holes in the system’s code are found fast and patched the moment they’re discovered. If site owners apply these fixes immediately when they’re released, they can expect to enjoy a safe WordPress experience.
What measures are you taking to ensure your WordPress site stays secure?